Ultimate Guide To Cloud Security
Online payroll providers are adapting, offering enhanced automation and improved user experiences to meet changing workforce needs.
Your comprehensive breakdown of everything related to securing your cloud environment.
What is Cloud Security?
Cloud Security refers to the measures, protocols, and technologies that protect cloud-based systems and data. As businesses increasingly rely on cloud infrastructure, the importance of robust Cloud Security has skyrocketed. This encapsulates not only data protection but also compliance with regulations, threat detection, and managing vulnerabilities within cloud environments. If you're looking to safeguard your cloud assets, understanding the full scope of cloud security is essential.
For a deeper dive into what Cloud Security encompasses, you can check out this informative piece from Google Cloud.
The Need for Cloud Data Protection
As data breaches continue to make headlines, maintaining Cloud Data Protection is critical. Organizations must prioritize securing sensitive information stored in cloud environments. This often involves encryption, access controls, and regular audits. Implementing effective cloud security solutions can ensure that your data is protected from unauthorized access and potential breaches.
Cloud Security Solutions: What Are Your Options?
There are myriad Cloud Security Solutions available, each tailored to specific needs in the cloud ecosystem. Whether it’s encryption tools, identity and access management, or vulnerability scanning services, having the right solutions in place is essential. Businesses often benefit from layering different solutions to improve their overall security posture.
Benefits of Using Cloud Security Services
Cloud Security Services facilitate the protection of cloud-based data and applications by providing structured approaches to securing environments. These services include continuous monitoring, threat intelligence, and incident response support. By utilizing these services, organizations can achieve compliance, streamline operations, and reduce their overall risk exposure.
Understanding Cloud Compliance
Navigating the landscape of regulatory requirements is vital for any cloud strategy. Cloud Compliance ensures that your cloud operations align with legal standards, industry regulations, and corporate policies. Establishing a compliance framework early can save headaches later, especially during audits. Make sure to assess which regulations apply to your organization and work with your teams to integrate compliance into your cloud security strategy.
The Importance of Cloud Threat Detection
Proactively identifying potential threats is paramount in today’s digital environment. Cloud Threat Detection technologies can analyze cloud activities in real-time to flag irregular behaviors or known attack signatures. Swift detection means faster response times and less risk of critical data loss or system compromise. Investing in robust detection systems can mean the difference between a quick mitigation and a devastating data breach.
Mastering Cloud Vulnerability Management
Cloud environments are not immune to vulnerabilities. Cloud Vulnerability Management is a systematic approach to identifying, assessing, and mitigating vulnerabilities in cloud infrastructure. Regular scanning and assessments are pivotal to understanding your risk landscape. By prioritizing vulnerability management, organizations can address weaknesses before they can be exploited by threat actors.
What is a Cloud Access Security Broker (CASB)?
A Cloud Access Security Broker, or CASB, acts as a gatekeeper between an organization’s on-premises infrastructure and cloud services. CASBs provide visibility into cloud application usage and enforce security policies across cloud platforms. This tool can greatly enhance the implementation of Cloud Security Posture Management by ensuring that users interact with cloud resources securely and compliant with organizational policies.
Cloud Security Posture Management (CSPM): A Foundation for Cloud Security
At the heart of any modern cloud security strategy lies Cloud Security Posture Management (CSPM). CSPM solutions enable organizations to continuously monitor their cloud environments for compliance violations and misconfigurations. By automating security assessments, CSPM helps teams enforce policies, thus improving overall security posture. Integrating CSPM into your operations is essential for maintaining a secure cloud environment.
For more details on CSPM and its significance, you can refer to this resource from IBM.
Conclusion
The landscape of cloud computing is ever-evolving, making Cloud Security more crucial than ever. With the right strategies and solutions in place—ranging from effective data protection to implementing a CASB and adopting CSPM—organizations can thwart threats and navigate the complexities of cloud security with confidence. Stay informed, stay secure, and embrace the cloud with awareness.

Related Posts

11 States Offering Free Solar Panels
Homeowners in eleven states can now get free solar panels, reducing energy costs and promoting sustainability.
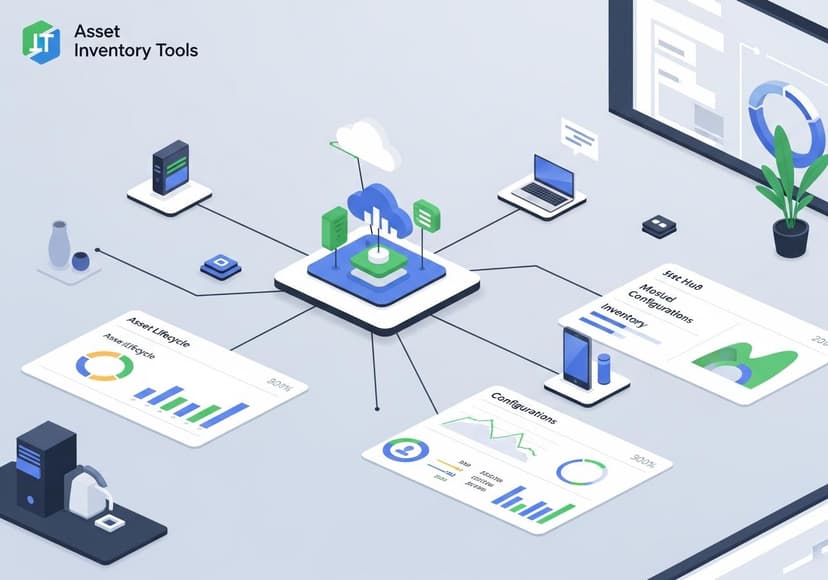
Asset Maintenance Management
Asset inventory tools streamline tracking, improving equipment lifecycle oversight and enhancing maintenance planning for optimized resource allocation.

Boosting Employee Engagement With Evaluation Software
The software improves employee performance through feedback, goal tracking, and development, ultimately enhancing workplace satisfaction and productivity.