Cloud Identity Management Short Overview
It centrally manages and secures digital identities. Access control and policy enforcement are key benefits.
What is Cloud Identity Management?
Cloud Identity Management (CIM) is a modern solution that allows organizations to manage user identities and access to digital resources seamlessly. Instead of relying on on-premises systems, CIM operates in the cloud, providing an efficient way to manage user authentication, authorization, and access control. With the growing trend of remote work and the need for secure access to corporate resources, Cloud Identity Management has become essential for businesses of all sizes.
The heart of CIM lies in its ability to streamline processes such as Single Sign-on, enabling users to access multiple applications with a single set of credentials. This not only enhances user experience but also minimizes security risks associated with password reuse. Furthermore, it simplifies Access Management, ensuring that the right individuals have the right level of access to various resources.
The Importance of Authentication and Authorization
In any security framework, the concepts of authentication and authorization play a critical role. Authentication verifies the identity of a user, ensuring that whoever tries to gain access is who they say they are. On the other hand, authorization determines what resources a user has permission to use. In the realm of Cloud Identity Management, implementing effective authentication methods is crucial to safeguard valuable assets.
Multi-factor Authentication (MFA) is a common approach that enhances security by requiring users to provide two or more verification factors to gain access. This additional step reduces the chances of unauthorized access, complementing the authorization process, and making it an essential element in cloud security. Organizations that prioritize robust authentication measures reduce the risk of data breaches, thus complying with various regulatory requirements.
Identity Federation for Seamless Access
Identity Federation allows users to utilize a single set of credentials across different organizations or platforms. This means that, for example, a user can log into their company's resources without needing separate credentials for each connected service. This capability not only promotes productivity but also enhances user satisfaction, making it an attractive feature of Cloud Identity Management.
With federated identities, companies can maintain a level of security while letting users access critical applications with ease. Partnering with providers like Okta can help organizations manage these federated identities effectively, enabling businesses to scale their operations while keeping security in check. As organizations collaborate with external partners, identity federation becomes integral to ensuring secure access without compromising compliance and governance.
Privileged Access Management: Protecting Critical Assets
Within the framework of Cloud Identity Management, Privileged Access Management (PAM) is essential for protecting sensitive resources. PAM involves managing and monitoring access for users who hold elevated privileges, such as administrators or IT personnel. These users often have access to critical systems and data, making them prime targets for attackers.
Effective PAM practices include managing the lifecycle of privileged accounts, implementing least privilege access, and continuously monitoring access activities. By integrating PAM into their overall identity strategy, organizations can further enhance their security posture while ensuring compliance with industry standards. This level of governance not only protects the organization but also builds trust among users and clients alike.
About Identity Governance and Compliance
Identity Governance is about ensuring that access rights are appropriate and managed correctly within an organization. Strong governance practices establish policies, processes, and controls, ensuring that user access aligns with regulatory and business requirements. By adopting effective governance strategies, organizations can minimize the risk of non-compliance, financial penalties, and reputational harm.
Compliance with standards such as GDPR, HIPAA, and SOX is critical for businesses operating in regulated industries. Utilizing cloud-based systems for Identity Governance allows organizations to implement automated processes that track and audit user access activities, ensuring transparency and accountability. The importance of compliance cannot be overstated, as it serves as a safety net against potential security breaches and legal ramifications.
The Role of Directory Services in Cloud Identity Management
Directory Services act as the backbone of identity management systems, storing identity information such as user attributes and access rights. In the context of Cloud Identity Management, these services provide a centralized repository of users, allowing for efficient management and retrieval of identity-related data. They are vital for syncing various applications in the cloud and ensuring that data remains consistent across platforms.
By leveraging cloud-based Directory Services, organizations can scale their identity management solutions without encountering the traditional challenges associated with on-premises systems. This transformation not only enhances the overall efficiency of access management but also contributes positively to the organization's security posture and compliance efforts. Implementing these services means better control over how user information is managed and accessed, providing a significant step forward in achieving comprehensive cloud security.
For in-depth insights into the world of Cloud Identity Management, check out additional resources such as the ID Management Playbook.

Related Posts

5 Ways To Improve Your Companys It Managed Services
Optimize IT managed services by focusing on automation, security, and proactive monitoring to enhance efficiency.
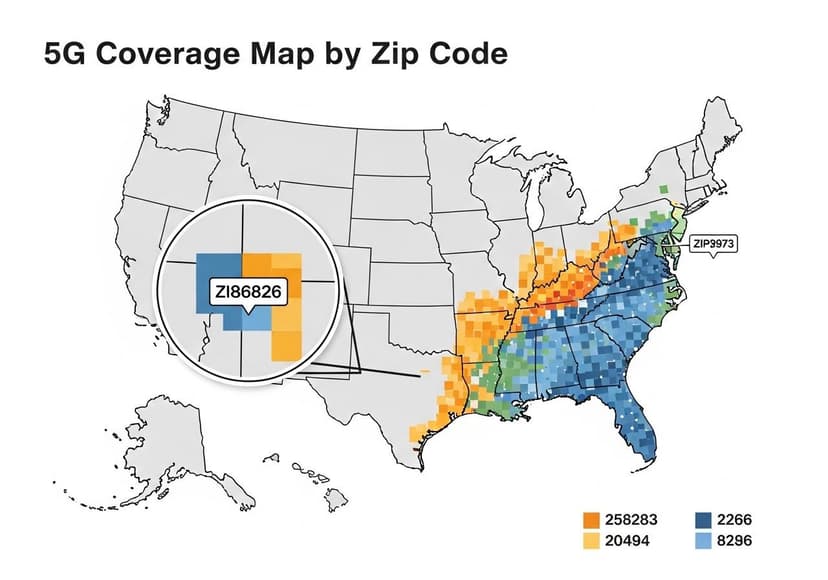
5G Coverage Map By Zip Code
Find detailed 5G coverage information by zip code, including availability and service quality.

5G Internet The Future Is Now
Enhanced speeds and connectivity redefine digital landscapes. Its impact spans industries, connecting everyone globally.